In 2026, the Salesforce landscape has shifted from basic CRM management to an “Agentic” ecosystem where autonomous AI agents handle complex workflows. While this drives efficiency, it creates a larger attack surface for your business data. At Aspire Software Consultancy, we recognize that securing your data is no longer a “one-and-done” configuration. It is a continuous strategic process. This guide explores the essential steps to protect your environment using the latest Salesforce security frameworks.
The Shift to Agentic Security
The introduction of autonomous agents has changed the user intent of security from simple login protection to complex interaction monitoring. When you begin a Salesforce Agentforce implementation, you are essentially giving AI the “keys” to your data. If those keys aren’t restricted, the risk of data leakage increases significantly.
Security in 2026 focuses on “Grounding.” This ensures that your AI agents only use the specific data they are authorized to see. At Aspire, our Salesforce consulting services focus on building these guardrails. We ensure that your AI doesn’t just work fast—it works safely within your established compliance boundaries.
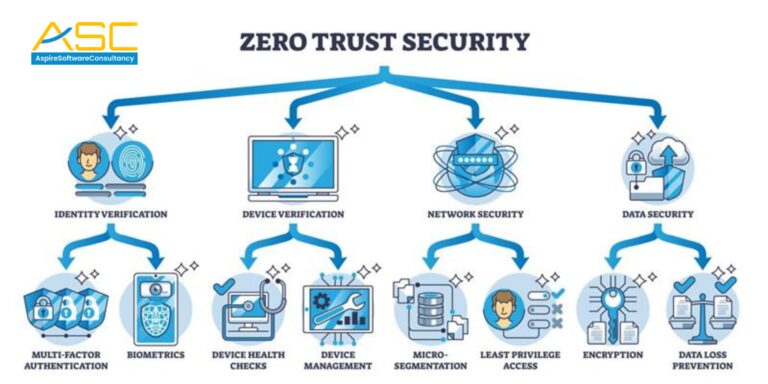
Implementing Zero Trust Architecture
The traditional perimeter-based security model is obsolete. Today, organizations must adopt a Zero Trust architecture. This means every user, device, and API call must be verified, regardless of whether they are inside or outside the network.
A Salesforce Sales Cloud expert will tell you that the “Principle of Least Privilege” (PoLP) is your best defense. In 2026, we focus on moving high-risk permissions away from standard profiles and into specific Permission Sets. This ensures that even if a credential is compromised, the “blast radius” is limited to only what that specific user needs to perform their role.
Advanced Encryption and Salesforce Shield
For enterprises requiring high-level compliance, Salesforce Shield remains the gold standard. It provides three critical layers of protection:
- Platform Encryption: Unlike standard encryption, this allows you to encrypt sensitive data at rest while preserving platform functionality like search and workflow.
- Event Monitoring: This provides deep visibility into who is accessing what data and from where. In 2026, AI-driven anomaly detection can alert your team to suspicious export activity in real-time.
- Field Audit Trail: This allows you to track the state and value of your data for up to ten years. This is essential for regulated industries like finance and healthcare.
Using Salesforce customization services, we can tailor these Shield components to trigger specific alerts when unusual patterns are detected, such as a bulk export of lead data at an unusual hour.
Multi-Factor Authentication (MFA) and Identity Cloud
By 2026, MFA is no longer optional; it is the baseline. However, the “User Intent” for security has evolved toward biometric and passwordless logins. Integrating Salesforce Identity Cloud allows for a seamless yet highly secure login experience. As a Salesforce consulting partner, we help businesses transition from outdated SMS-based MFA to more secure options like hardware keys or built-in authenticators.
The Importance of Regular Security Audits
Many businesses assume their Org is secure because they haven’t had a breach yet. However, “Security Debt” accumulates over time as new fields are added and old users aren’t deactivated. A professional audit involves:
- Checking the “Health Check” score within Salesforce.
- Reviewing external sharing settings on sensitive objects.
- Auditing third-party AppExchange integrations.
- Verifying that Salesforce Agentforce implementation logs are being reviewed.
Why Choose a Certified Partner?
Navigating these complex security layers requires specialized knowledge. Choosing a certified Salesforce consulting partner ensures that your security posture is not just a checkbox but a competitive advantage. At Aspire Software Consultancy, our team provides comprehensive reviews that align with your specific business goals. Whether you are a small startup or a global enterprise, we ensure your Salesforce customization services don’t create “backdoors” for malicious actors.




